In today’s fast-paced digital world, software development needs to be efficient and secure. As organizations accelerate the delivery of software applications, they also face an ever-growing threat landscape. To combat these threats, integrating threat modeling with DevOps has become a best practice for building secure software.
What is DevOps?
DevOps is a set of practices that combines software development and IT operations to deliver high-quality software more efficiently. The DevOps approach emphasizes collaboration, communication, and automation throughout the software development life cycle.
What Do You Mean by Threat Modeling?

Threat modeling is a structured approach to identifying and evaluating potential security threats to a system or application. By analyzing the system architecture, data flows, and potential attack scenarios, developers can identify vulnerabilities and implement security controls to mitigate risks.
Why Integrate Threat Modeling with DevOps?
Integrating threat modeling with DevOps allows organizations to identify and mitigate security risks early in the software development life cycle. By integrating security into the DevOps pipeline, security teams actively collaborate with software development teams to ensure that security protocols are incorporated into the application right from the beginning.
Without threat modeling, security risks may go unnoticed until later in the development process, making them more costly and time-consuming to remediate. With the integration of threat modeling into the DevOps pipeline, organizations can proactively address security risks and reduce the likelihood of data breaches or cyber-attacks.
According to a study by IBM, the average cost of a data breach is $3.86 million, and the average time to identify and contain a breach is 280 days. Integrating threat modeling into the DevOps pipeline can help reduce these costs and time frames significantly by addressing security risks early on in the development process.
Also Read: What is Containerization in DevOps?
What Makes DevOps & Threat Modeling a Perfect Match
DevOps, a set of practices that combines software development and IT operations, is a proven way to streamline software delivery. Threat modeling, on the other hand, is a structured approach to identifying and evaluating potential security threats to a system or application. Together, DevOps and threat modeling offer a powerful combination for building secure software efficiently.
Key Components of DevOps
Consequently, Agile development, Continuous Integration/Continuous Deployment (CI/CD), Security as Code, and Shift Left Security are some of the key components of DevOps. These enable organizations to deliver software faster and more securely.
- Agile Development – Agile development emphasizes collaboration, flexibility, and rapid iteration, allowing organizations to quickly respond to changing customer needs and market demands. By incorporating threat modeling into the Agile development process, security teams can work closely with developers to identify potential security risks early in the development cycle, reducing the likelihood of vulnerabilities and security breaches.
- CI/CD – Continuous Integration/Continuous Deployment is a set of practices that automates the software delivery process, enabling organizations to deliver software more frequently and with greater reliability. By integrating security testing into the CI/CD pipeline, organizations can identify security vulnerabilities and flaws in the code early in the development cycle, reducing the risk of security breaches and enabling faster remediation.
- Security as Code – Security as Code is a practice that emphasizes the integration of security controls and processes into the software development life cycle. By automating security controls and embedding them into the code, developers can ensure that security is built into the application from the outset. Consequently, reducing the likelihood of vulnerabilities and security breaches.
- Shift Left Security – Shift Left Security integrates security testing and evaluation early in the software development life cycle. By shifting automated security testing to the left, organizations proactively identify and address potential security risks in the initial stages of development. As a result, this approach reduces the likelihood of susceptibilities and security violations, stimulating robust software security.
By incorporating these practices into the DevOps project, organizations can build and deliver software faster and more securely. The combination of DevOps and threat modeling allows organizations to identify and remediate potential security risks at the first go. Nonetheless, ensuring that software is built with security in mind.
Read More: Increase Business Agility with DevOps and Cloud Consultation
5 Steps to Implementing Threat Modeling with DevOps
Implementing threat modeling with DevOps involves a structured process to identify and mitigate security risks throughout the software development life cycle. As a matter of fact, the following steps can help organizations successfully integrate threat modeling into their DevOps pipeline:
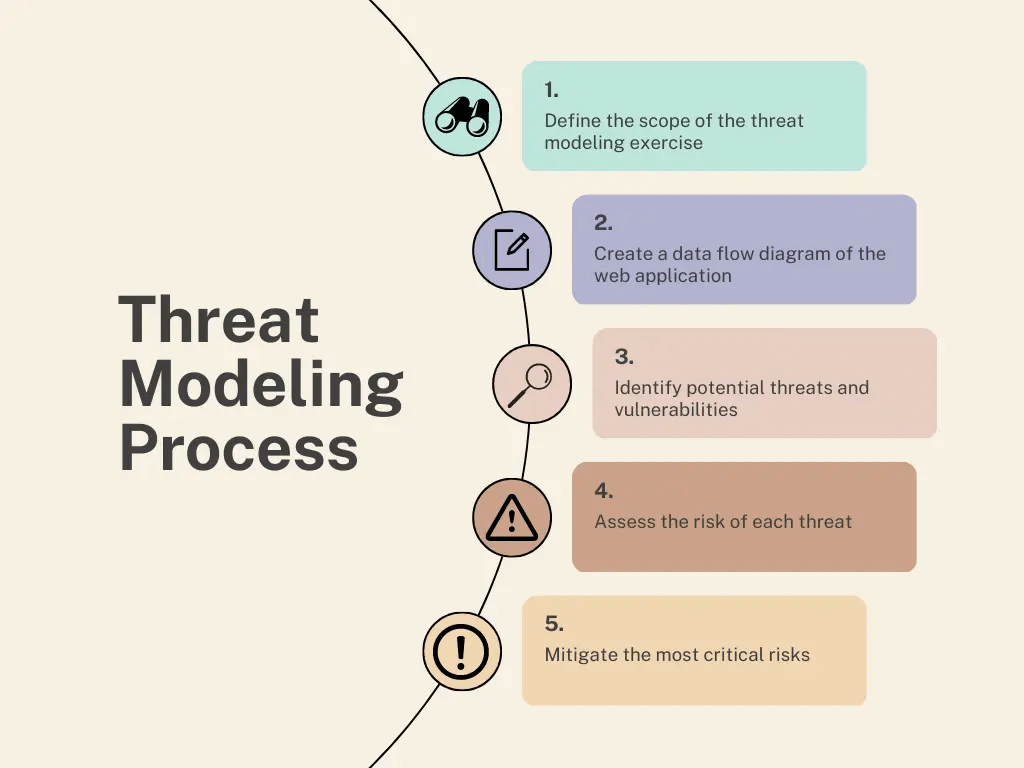
1. Identify Assets and Scope
The initial step in implementing threat modeling with DevOps is to identify the assets to be protected and determine the system’s scope. This includes identifying critical components, securing sensitive data, and defining the system’s boundaries. By defining the scope, developers can narrow their focus on areas of high risk and potential vulnerabilities. Thereby, making the process more efficient.
2. Develop Architecture Diagrams
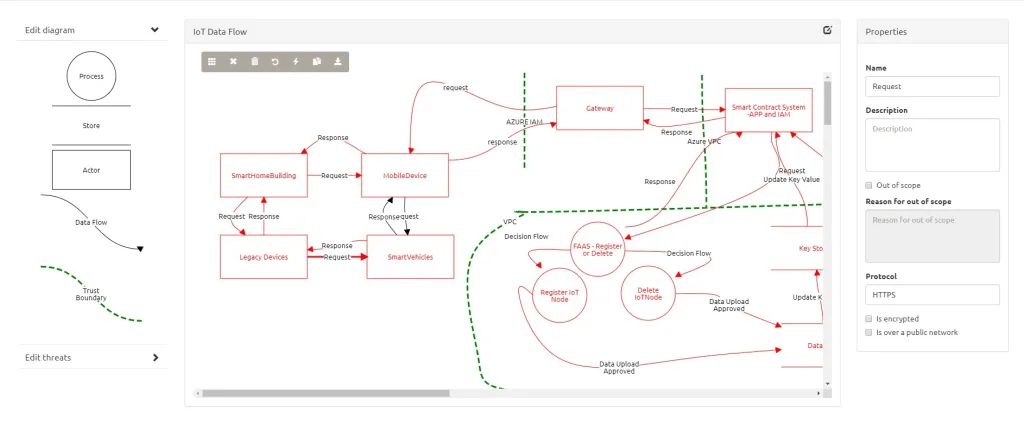
After identifying the scope, the next step is to develop architecture diagrams to visualize the system and its interactions. This helps in identifying potential vulnerabilities and attack vectors. In any case, developers can use tools like Microsoft’s Threat Modeling Tool or OWASP Threat Dragon to create architecture diagrams easily.
Microsoft Threat Modeling Tool is a widely used, free tool in the industry for threat modeling. This tool actively enables you to create data flow diagrams of your web application, effectively identifying potential threats and vulnerabilities. Additionally, you can assign a risk level to each threat and seamlessly prioritize them based on their impact on your application. Furthermore, the tool provides actionable recommendations for mitigating each risk, empowering you to enhance the security of your application effectively.

OWASP Threat Dragon is a useful open-source tool for creating and managing threat models for web applications. With this tool, you can easily create data flow diagrams to identify possible threats and vulnerabilities. After identifying threats, you can assign a risk level to each and prioritize them according to their impact on the application. Additionally, the tool suggests ways to mitigate each risk.
3. Identify Threats and Potential Impacts
This step involves identifying potential threats and their impacts on the system. Once the vulnerabilities are identified, it is important to assess the potential impact of each threat to the system. Correspondingly, threats can be identified using various techniques.

- STRIDE: A model for identifying and categorizing threats based on Spoofing, Tampering, Repudiation, Information disclosure, Denial of service, and Elevation of privilege.
- DREAD: A framework for assessing the severity of a potential vulnerability based on Damage potential, Reproducibility, Exploitability, Affected users, and Discoverability.
- PASTA: A methodology for attack simulation and threat analysis that emphasizes the importance of context and process.
- OCTAVE: An evaluation methodology for identifying and addressing operational risks to critical assets and vulnerabilities.
- TRIKE: A risk-based approach to threat modeling that includes a unique implementation and risk-modeling process.
- VAST: A visual, agile, and simple approach to threat modeling that emphasizes collaboration and practicality.
4. Prioritize and Rank Threats
After identifying the potential threats and assessing their impact, the next step is to prioritize and rank the threats based on their severity. Besides, this process aids in identifying the most critical threats that require immediate attention. In fact, prioritizing and ranking assist in resource allocation and determining which threats can be addressed at a later stage.
5. Develop and Implement Mitigations
The final step is to develop and implement mitigations to address the identified threats. This could involve implementing security controls, adding additional layers of protection, or changing the architecture of the system to eliminate vulnerabilities. It is important to regularly review and update the mitigations to ensure that they continue to be effective.
Moreover, mitigations can be technical, procedural, or a combination of both. For example, a technical mitigation may involve implementing secure coding practices to prevent injection attacks, while a procedural mitigation may involve training developers and users on best practices for secure coding and password management.
By following these five steps, organizations can effectively implement threat modeling with DevOps to identify and address potential security threats in their systems. Furthermore, this practice helps minimize the risk of security breaches and ensures the protection of the organization’s critical assets.
Best Practices for Integrating Threat Modeling with DevOps
-

Source: comparitech.com Collaboration between development, operations, and security teams – Collaboration is essential for effective threat modeling. It helps in identifying potential threats and vulnerabilities at every stage of the software development lifecycle. DevOps teams need to collaborate closely with the security teams to integrate security requirements into the development process. Subsequently, this collaboration will ensure that potential threats are identified early and addressed promptly. Furthermore, mitigating the risk of them becoming more significant issues.
- Automation of threat modeling processes – Automation can make the threat modeling process more efficient and effective. Automation can help to reduce the time required for threat modeling and increase accuracy. It can also help to identify potential threats and vulnerabilities that may be missed in a manual process. By using automation, organizations can ensure that the software they are building is secure and reliable.
- Regular reviews and updates – Threat modeling is not a one-time event. It is an ongoing process that requires regular reviews and updates. Threats and vulnerabilities can change over time, and it is essential to stay up-to-date with the latest threats and vulnerabilities. In addition, this helps identify new threats and vulnerabilities and ensure that existing ones are addressed.
- Integration with other security tools and processes – Integrating threat modeling with other security tools and processes can help to create a more robust security infrastructure. Likewise, this can help to ensure that software is secure before it is deployed.
Also Read: Security Will No Longer Be an Afterthought in DevOps Pipelines
Challenges and Solutions in Integrating Threat Modeling with DevOps
As with any new process, integrating threat modeling with DevOps can present several challenges. However, with the right approach, these challenges can be overcome. Here are some of the common challenges and their solutions:
Overcoming Resistance to Change
One of the primary challenges in integrating threat modeling with DevOps is resistance to change from team members. Some may be hesitant to adopt a new process or feel that it will slow down their workflow. To overcome this, it’s essential to communicate the benefits of threat modeling and involve team members in the process. Showing real-life examples of how this has helped improve security can also help convince team members.
Read This: Benefits of Implementing DevOps to Enhance Business Workflow
Incorporating Threat Modeling into Existing Processes
Another challenge is incorporating threat modeling into existing processes without disrupting the development and deployment cycles. The solution to this is to integrate it into the existing tools and processes used by the team. For example, when we embed the same into the CI/CD pipeline, we ensure that we integrate security into every step of the process. However, without adding any additional steps.
Addressing the Need for Specialized Skills and Knowledge
Another challenge is the need for specialized skills and knowledge to conduct effective modeling. The solution to this is to provide training and resources to team members to develop these skills. Additionally, leveraging automated tools can help simplify the process and reduce the need for specialized skills.
Leveraging Threat Modeling to Improve Overall Security Posture
Finally, a key challenge is to leverage threat modeling to improve the overall security posture of the organization. The solution to this is to conduct regular threat model reviews and updates to ensure that the organization stays ahead of evolving threats. Integrating this with other security tools and processes can also help improve the overall security posture.
Know More: Emerging DevOps Trends
The Crux of the Matter
Integrating threat modeling with DevOps is not just a necessary step but a crucial one toward building secure and resilient software applications. Following best practices such as collaboration, automation, regular reviews, and integration with other security tools can significantly improve an organization’s DevOps consulting services. This integration offers numerous benefits, including improved security posture, reduced costs associated with security incidents, and increased customer trust. However, there are challenges to overcome, such as resistance to change, skill gaps, and process integration, to ensure successful implementation.
As the software development lifecycle continues to evolve, there are ample opportunities for further integration and improvement in this area. At Binmile, we understand the importance of threat modeling in software development services and offer comprehensive solutions that encompass all aspects of software security. With our expertise, you can seamlessly integrate threat modeling into your DevOps processes and stay ahead of emerging threats. Reach out to us for all your software solution needs and ensure that your applications are secure and resilient.