Cyberattacks are no longer rare disruptions. They are constant, evolving, and increasingly expensive. According to IBM’s Cost of a Data Breach Report of 2025, the global average cost of a data breach reached $4.44 million. This rising cost highlights a clear reality that reactive security is no longer enough.
Staying competitive requires organizations to look beyond defensive strategies, making cyber threat intelligence a key capability for businesses. In this blog, we will explore the meaning of cyber threat intelligence, the applicability of cyber threat intelligence in business, the advantages, the types of cyber threat intelligence, the challenges that cyber threat intelligence faces, and the ways to measure the return on investment of successfully implementing cyber threat intelligence for businesses.
What is Cyber Threat Intelligence and Why It Matters
Cyber threat intelligence refers to the process of collecting, analyzing, and interpreting data related to potential or existing cyber threats. Traditional systems wait until an attack happens and focus on defending against attacks. With cybersecurity threat intelligence, organizations focus on not allowing attacks to happen in an anticipatory way.
Cyber intelligence starts with basic information and derives meaning from it. Enterprises get to learn from attackers, understand where the weaknesses are, and improve their cybersecurity intelligence. This is the main goal.
For enterprises with sensitive, financial, or operational data, this intelligence is an early alert. This helps security move from a more defensive position to an offensive position.
Understanding the Cyber Threat Intelligence Framework
A structured threat intelligence framework ensures that intelligence is not just collected but also used effectively. It typically follows a lifecycle approach:
1. Data Collection
Early in the process, companies want to avoid filtering data to stay relevant. They gather data from system logs, network communications, potential threats from the web, open-source intelligence, and even dark web trackers.
2. Data Processing
The data that has been collected is, of course, the data that has been processed. Information is taken from logs and old records so that the data is in its most useful state, and the current collected information has been adjusted.
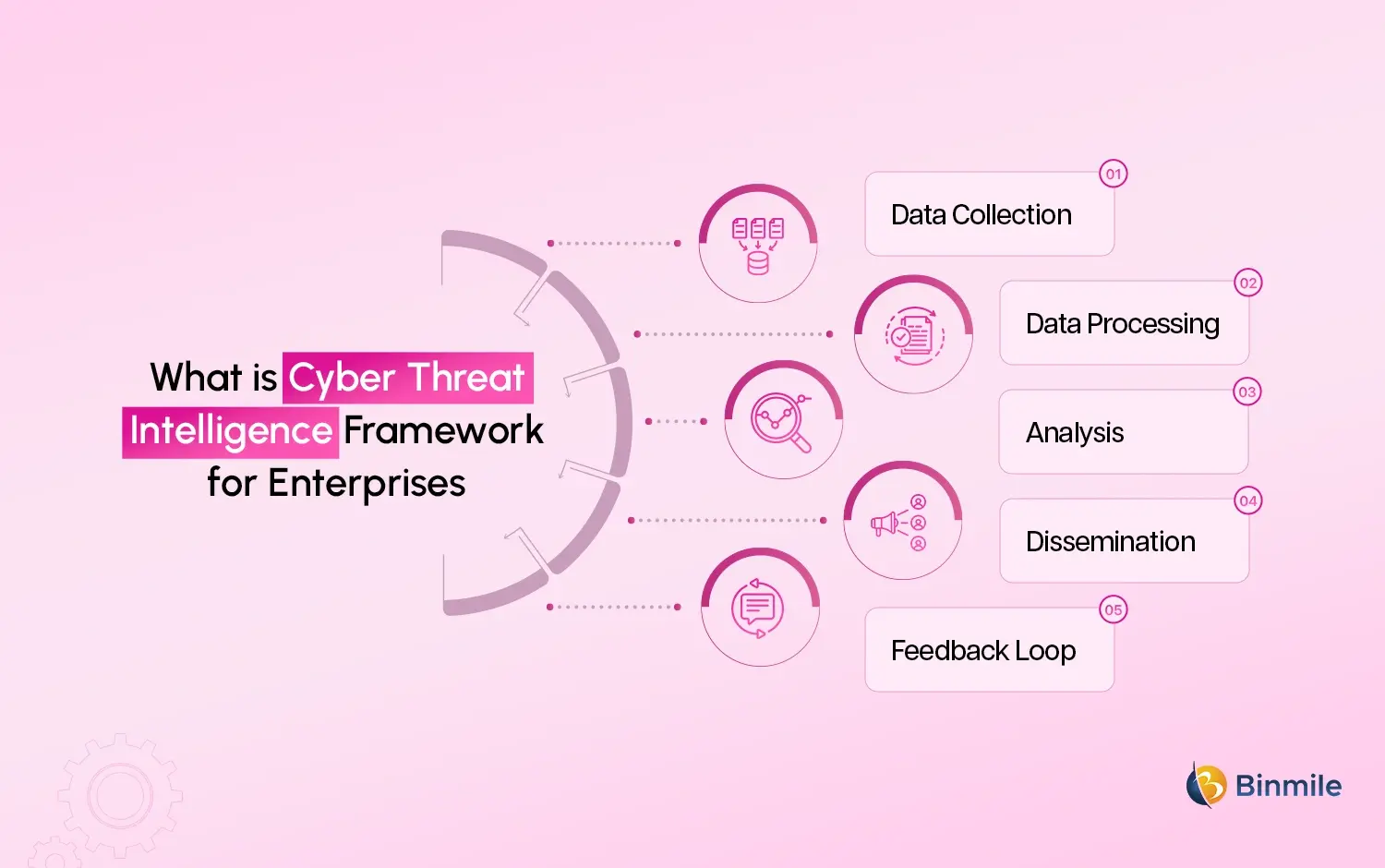
3. Analysis
This is the most important step in the collection process. It is the step in which the most input is evaluated and processed. AI, or even modern computational systems, are used to process this data.
4. Dissemination
It is important to be clear about the final stages of the process. Because of this, choices can be made much faster, and collaborations can be performed much more effectively. Investing in this process for the best data available can eliminate potential threats.
5. Feedback Loop
The external information keeps the internal systems dynamic. Investment in the system is one of the systems of intelligence, and this feedback informs the system to improve data collection. Because of this, the data remains relevant to the current available data.
What are the Key Benefits of Cyber Threat Intelligence for Enterprises
The benefits of cyber threat intelligence are much broader than attack prevention. It focuses on attack detection, breach avoidance, and moving security from a reactive strategy to a proactive one.
When security teams focus on real-time data, they are able to respond much faster, which reduces downtime and overall improves the resiliency of the organization. This also leads to better resource allocation by the decision-making leaders and more robust security plans aligned with the organization’s primary worries.
From a financial viewpoint, prevention is most certainly better than a cure. Sophisticated cyber intelligence solutions lead to better financial loss mitigation, and the heightened visibility and control simplify regulatory compliance.
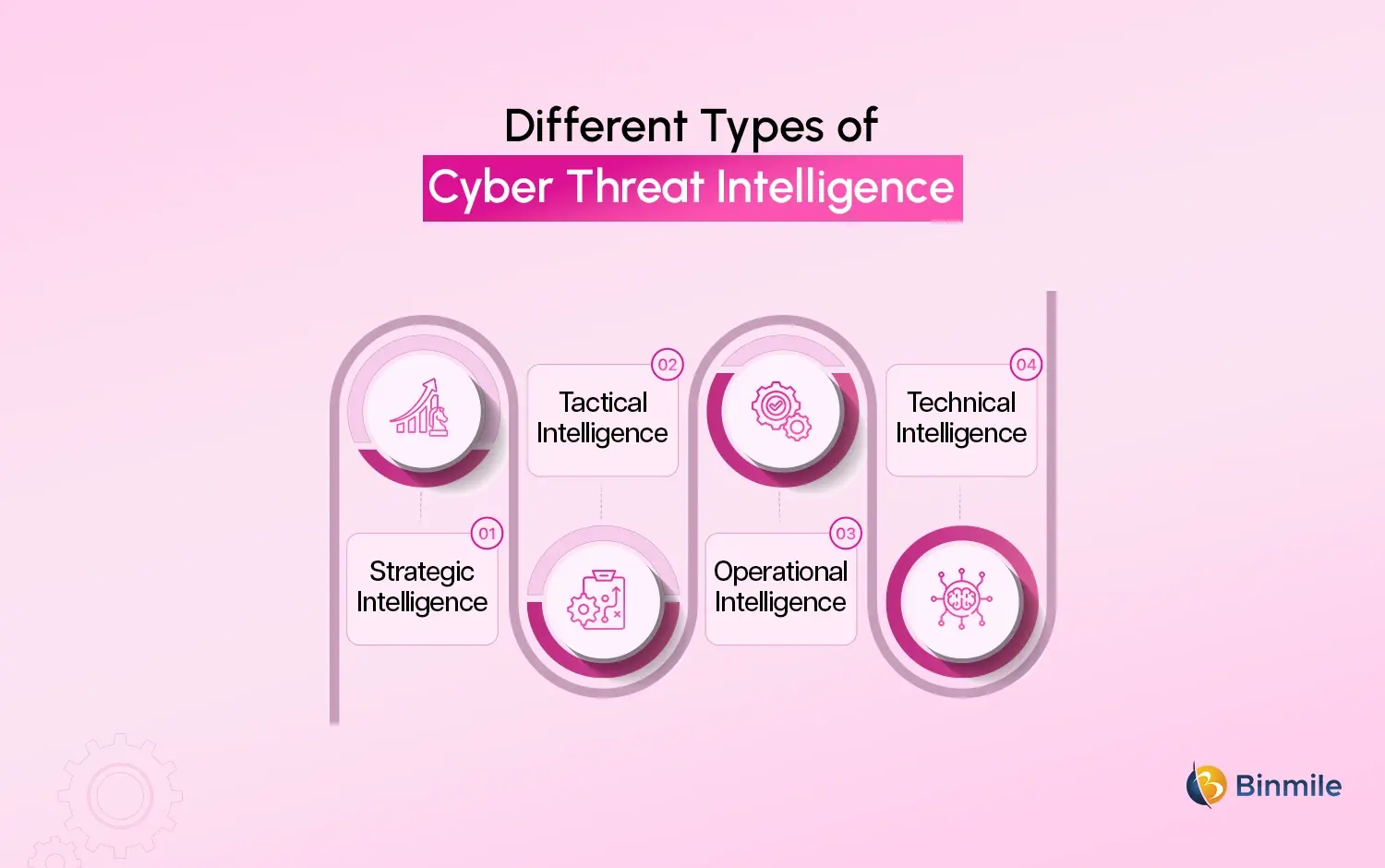
What are the Types of Cyber Threat Intelligence
Understanding the different types of cyber threat intelligence helps enterprises use them more effectively. Each type serves a unique purpose:
-
Strategic Intelligence
More of a ‘big picture’ view. It provides leaders with an understanding of different trends, potential risks, and their potential long-term impacts. This can assist with decision-making and the overall formulation of policy.
-
Tactical Intelligence
This is concern to define the threat actors, the methods of attack, and the instruments involved. It supports security staff in appreciating the mechanism of the attack.
-
Operational Intelligence
This provides insight into an ongoing attack in real time. This is of value to the incident response teams.
-
Technical Intelligence
This consists of data points such as an IP address, specific malware signatures, and particular URLs. It is the basis for instituting or layering immediate defenses.
Using a combination of these types ensures a well-rounded cyber risk intelligence strategy.
What are Cyber Threat Intelligence Real-World Use Cases Across Industries
Cyber threat intelligence is not limited to one industry. Its applications are wide and practical.
-
Cybersecurity in Fintech
Fraud detection, phishing, account takeovers, and financial crimes prevention come under cybersecurity in fintech, all of which rely on intelligence to analyze and identify fraudulent activities.
-
Modern Application Security
Thanks to the intelligence integrated into the modern application security, possible weaknesses and lack of potential threats before and during the phases of construction can easily be determined.

-
Zero Trust Security Model
The Zero Trust security model of intelligence regarding threats supports the constant monitoring of activities of the users, the devices, and the activities users employ.
-
Threat Modelling with DevOps
The predictive and defensive threat modeling with DevOps of potential threats is achievable by utilizing intelligence integrated in the stages of construction of the Development pipelines.
-
Artificial Intelligence as a Service and AI Risks
The predictive and defensive modeling of potential threats becomes more effective when enterprises leverage Artificial Intelligence as a Service within their development pipelines.
Cyber Threat Intelligence Tools and Technologies
To implement CTI cybersecurity, enterprises rely on various tools and platforms. These tools automate data collection, analysis, and reporting.
| Tool Type | Purpose |
|---|---|
| Threat Intelligence Platforms (TIPs) | Aggregate and analyze threat data |
| Security Information and Event Management (SIEM) | Monitor and analyze security events |
| Endpoint Detection and Response (EDR) | Detect threats on devices |
| Dark Web Monitoring Tools | Track leaked data and potential threats |
| AI-Based Security Tools | Predict and prevent attacks using machine learning |
These tools form the backbone of modern cyber intelligence solutions.
What are the Challenges of Cyber Threat Intelligence
The challenges of cyber threat intelligence present considerable benefits, but poorly trained employees gravely hinder this potential in completing the split with fragmented intelligence.
Assuredly, the use of cyber threats is without its hardships, and the integration of prior cyber intelligence models is without fragmented challenges in integrating intelligent models into existing integration models.
In many organizations, integrating existing Cybersecurity models without cyber threats creates more cyber threats than are addressed by the integrated models. Integrating Cyber intelligence with previously existing threats is also challenging without integrating existing models in cyber threats.
Want to reduce cyber risks while improving response time and operational resilience for your business?

What is the Measuring ROI of Cyber Threat Intelligence
Enterprises often ask whether investing in cyber threat intelligence is worth it. The answer lies in understanding ROI beyond just numbers.
-
Key Metrics to Consider
An effective system has a clear reduction in the number of security incidents over time. The quicker the responses are to incidents, the more operational impact they minimize. Along with improved compliance and avoidance of the costs associated with financial losses and penalties, lower recovery costs are also a benefit. Reduced downtime means that business continuity is protected and, therefore, also protects productivity and the revenue associated with it.
-
Example Scenario
An enterprise that lacks intelligence may take days to realize there is a breach. The company would incur tremendous losses. An intelligent system would realize the breach in a matter of hours and would decrease losses tremendously.
When thinking about ROI, savings are the least of it. What is more important is that the company has developed resilience and a trust in its long-term stability.
How Enterprises Can Get Started with Cyber Threat Intelligence
Adopting cyber threat intelligence does not require a complete overhaul. A structured approach works best.
Step 1: Assess Current Security Posture
Evaluating the current security systems involves evaluating the current systems, finding existing vulnerabilities, and breaking down the biggest threats. In order to utilize the intelligence successfully, it is imperative to have this knowledge.
Step 2: Define Objectives
After all of this is determined, the businesses need to establish goals. For example, some may want to focus on more efficient threat detection systems, while others may want to focus on less operational risk through more regulatory compliance. Improved specificity creates more defined and better overall goals.
Step 3: Choose the Right Tools
After establishing goals, the next step is picking the appropriate tools. Not all tools fit the needs of all businesses, and therefore, an assessment of the current goals along with the existing infrastructure is required. With the right tools, operational intelligence can become action-oriented.

Step 4: Build Skilled Teams
Forming seasoned teams is also imperative. Whether it be through hiring or training, organizations require people with cyber threat analysis knowledge to be able to utilize and interpret the intelligence. Adding the right technology to an organization with untrained staff will yield no benefits.
Step 5: Integrate with Existing Systems
When existing systems have the right tools implemented into them, there will be better intelligence flows and, therefore, better overall organizational visibility. When systems communicate with each other, there is improved decision-making.
Step 6: Continuously Monitor and Improve
Once all of these steps have been completed, there will be systems that will become outdated. Because of this, it is critical to keep improving the systems. Due to the rapid rate at which cyber threats develop, there must be some type of strategy to counter the threats. Ultimately, the systems will be more effective and therefore able to withstand more threats to cyber intelligence.
The Role of AI and Automation in Cyber Threat Intelligence
Modern cyber intelligence is heavily powered by AI and automation. These technologies enhance efficiency and accuracy.
Modern intelligence is good for predicting future threats and providing overall improvement of systems. Less human effort is needed and can enhance productivity.
AI is not perfect, and it is not a good idea to solely rely on it. Great mistakes in the process can happen, and it is necessary to govern and monitor the process to ensure it is not misused.
Looking to strengthen your enterprise security with smarter threat insights and proactive defense strategies?

Where Binmile Fits into Your Cyber Threat Intelligence Journey
Building an effective cyber threat intelligence system requires more than just tools. It needs the right combination of strategy, technology, and execution. This is where a partner like Binmile can quietly make a difference.
With expertise across cybersecurity practices, Modern Application Security, and Threat Modelling with DevOps, Binmile helps enterprises design intelligence-driven security systems that align with business goals. Instead of offering generic solutions, the focus remains on creating tailored frameworks that integrate seamlessly with existing infrastructure.
Whether it is strengthening a Zero Trust security model, addressing AI risks, or building scalable cyber intelligence solutions, the approach is always practical and results-driven. The goal is not just to implement intelligence but to make it a core part of how enterprises operate securely and confidently.
Frequently Asked Questions
Cyber Threat Intelligence is the process of collecting and analyzing threat data to predict and prevent cyberattacks. It is critical because it helps enterprises move from reactive security to proactive defense, reducing risks and improving overall security posture.
It enables proactive threat detection, faster incident response, improved decision-making, cost savings, and better compliance. Enterprises can reduce vulnerabilities and strengthen their security systems using actionable insights derived from intelligence.
Yes, by identifying threats early and preventing breaches, enterprises can avoid high recovery costs, legal penalties, and operational disruptions. Early detection significantly reduces the financial and reputational impact of cyber incidents.
Threat intelligence provides insights into attacker behavior, emerging threats, and vulnerabilities. This helps organizations stay prepared, make informed decisions, and implement stronger defenses against evolving cyber risks.
Start by assessing your current security posture, defining clear objectives, choosing suitable tools, building skilled teams, and integrating intelligence into existing systems. Continuous monitoring and improvement are essential for long-term success.
Yes, modern cyber threat intelligence relies on AI and automation to analyze large datasets, identify patterns, and predict threats. These technologies enhance speed, accuracy, and efficiency in detecting and responding to cyber risks.